(rev. July 4, 2015)
Notes On Chapter 30
-- Network Management (SNMP)
- 30.1 Introduction
- Conceptual model for network management
- Scope of network management activities
- Importance and difficulty of network management
- Network management technologies
- Paradigm used by network management systems
- A specific example of a network management protocol
- 30.2 Managing an Intranet
- A network manager (aka network administrator) is responsible for
maintaining all facets of a computer network.
- This can be difficult because the networks are often large,
and ever-changing collections of heterogeneous hardware and
software.
- Network software and/or hardware may be able to compensate for some
failures, which may make it difficult for the network manager to detect
the underlying problem.
- 30.3 FCAPS: The Industry Standard Model
- The industry standard model is derived from recommendation M.3400
of the International Telecommunications Union (ITU). The model is called
FCAPS, which stands for Fault detection and correction,
Configuration and operation, Accounting and billing,
Performance assessment and optimization, and
Security assurance and protection.

- Fault Detection and Correction: This is a major concern of the manager. It involves
investigative work to determine the nature of the problem from the given failure reports.
- Configuration and Operation: It is a challenge to maintain consistent configurations
on a large number of devices or software modules.
- Accounting and Billing: For correct billing, it may be necessary to monitor
the usage of each customer.
- Performance Assessment and Optimization: Diagnostic assessment has to do with maximizing
utilization of existing resources, and trend assessment deals with finding ways to increase
performance to match future needs.
- Security Assurance and Protection: Managers must consider multiple protocol layers and devices,
as well as continual development of new threats.
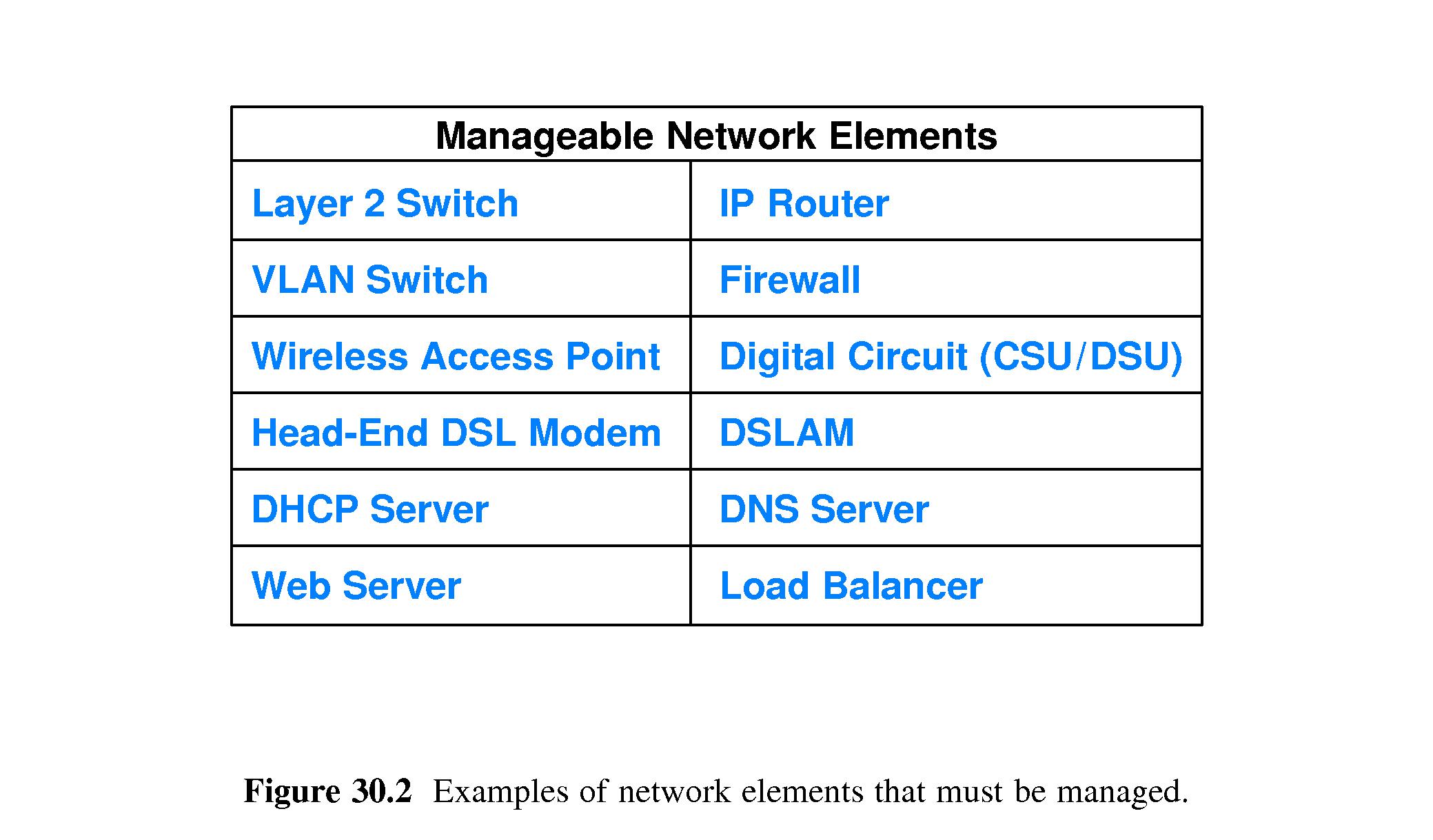
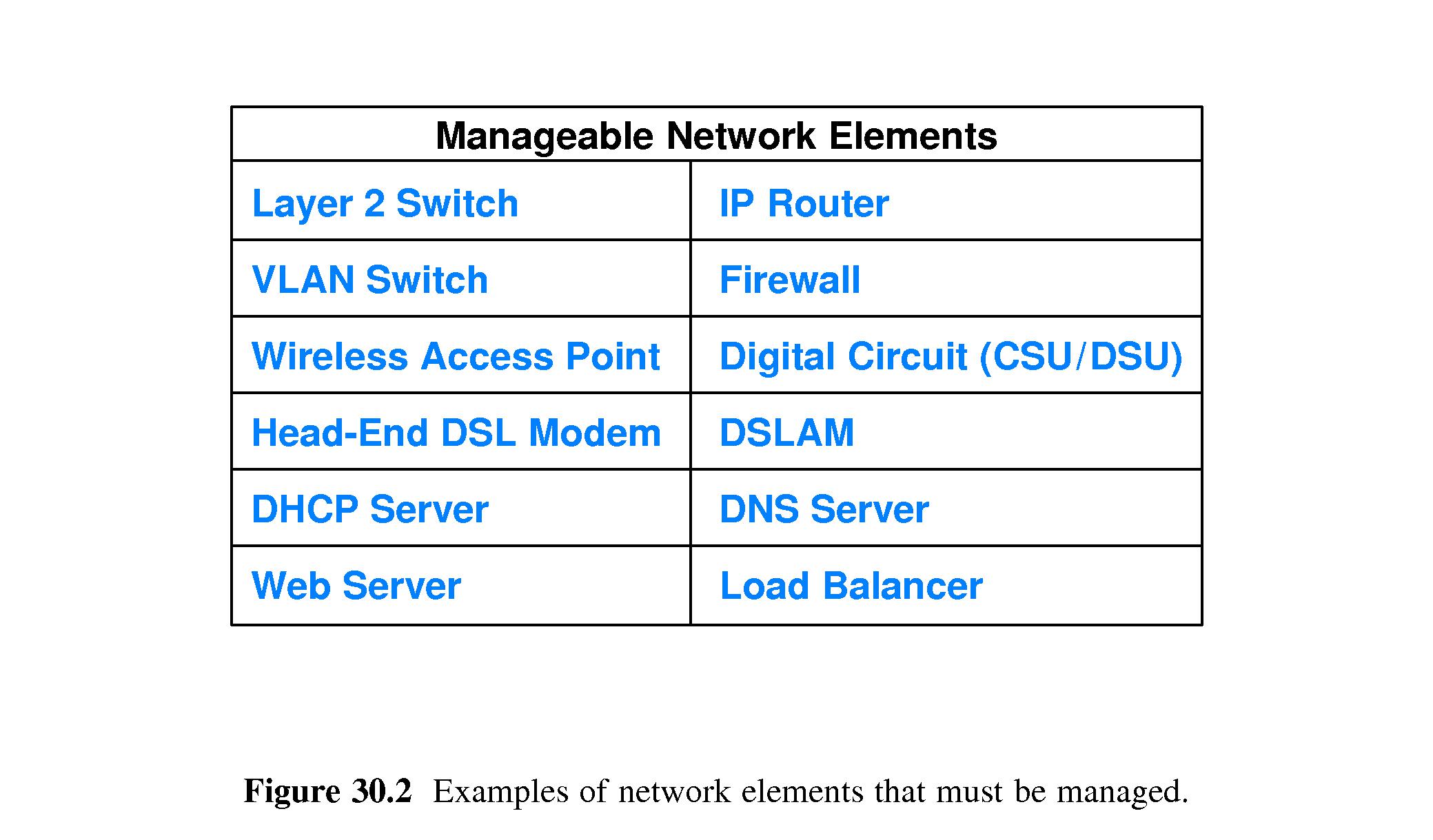
- 30.4 Example Network Elements
- A network element is any network device, system, or mechanism that can be managed.
The table lists examples.
- The industry definition of element management includes configuration and operation of
individual network elements, but not higher functions that configure and operate sets
of elements.
- Therefore it is an error-prone process to configure sets of elements one at a time.
- 30.5 Network Management Tools
- Management Tool Categories
- Physical Layer Testing - e.g. carrier sensor testing & wireless strength meters
- Reachability and Connectivity - e.g. ping
- Packet Analysis - e.g. Wireshark
- Network Discovery - probe & map network
- Device Interrogation - access each element
- Event Monitoring - e.g. devices send alerts when threshold is crossed
- Performance Monitoring - e.g. plots of performance over time
- Flow Analysis - e.g. monitor changes in specific kinds of traffic
- Routing and Traffic Engineering - control configuration of routing update protocols,
configuration and monitoring of MPLS tunnels
- Configuration - e.g. install/change configuration of (multiple) elements
- Security Enforcement - e.g. security policy configuration and monitoring
- Network Planning - e.g. linear programming algorithms to optimize architecture
- 30.6 Network Management Applications
- Network management software is generally client/server,
at the application level, run on the production network,
using conventional transport protocols like UDP and TCP.
- Human managers run client software when they want to access
elements, but these special-purpose clients are called managers.
- The servers that respond to managers are called agents.
- Typically the use of the production network for network management
works well, though some special backup access modes can be desirable.
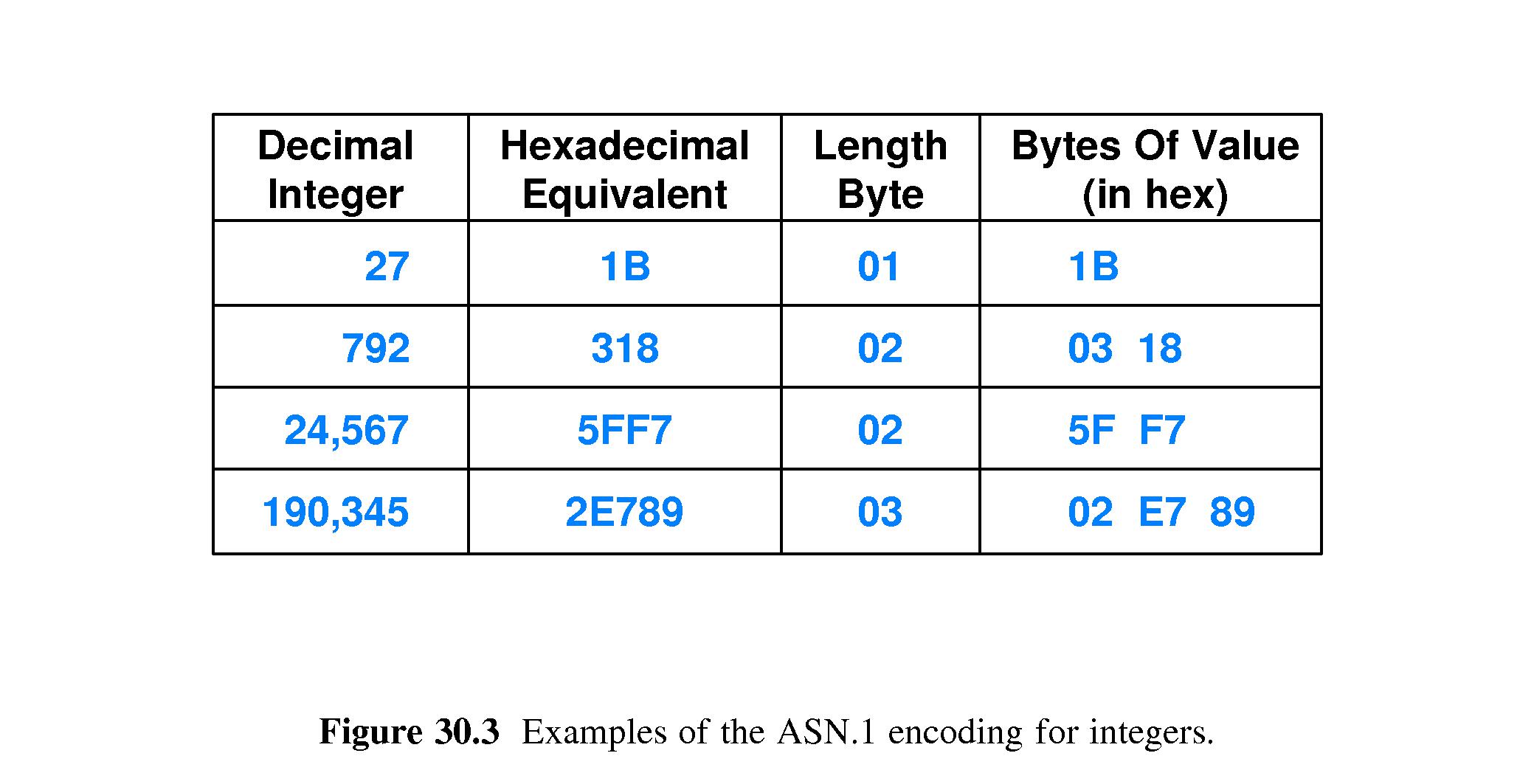
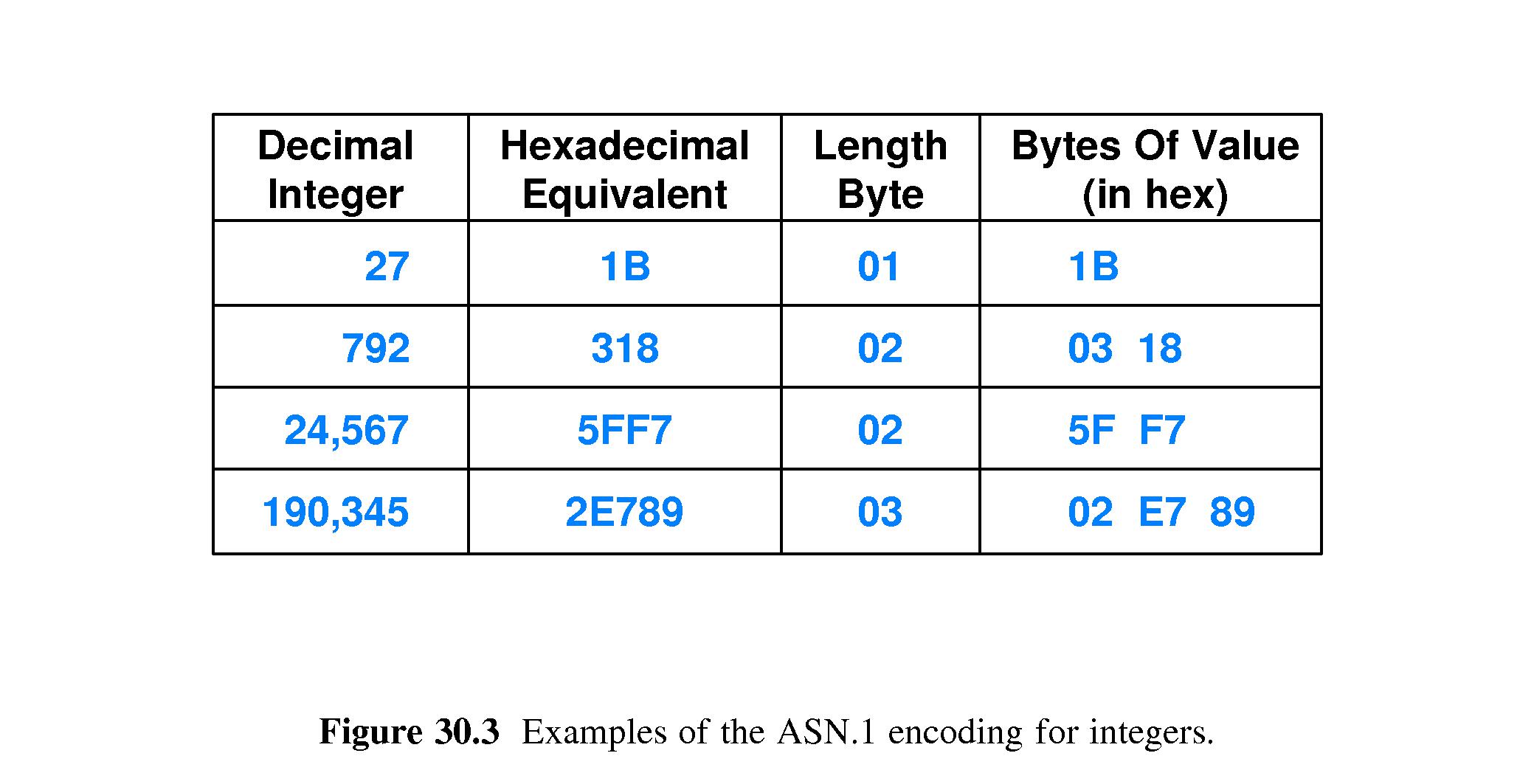
- 30.7 Simple Network Management Protocol
- SNMPv3 is the standard protocol for communication between network
managers and agents (clients & servers). The requests and replies
are encoded in Abstract Syntax Notation.1 (ASN.1).
- 30.8 SNMP's Fetch-Store Paradigm
- SNMP follows a paradigm of fetching values from objects and storing values to them.
- It is typical to fetch variable values containing status information.
- Control operations are accomplished as side-effects of storing values.
- It must be remembered that managers perform fetch/store as communication with agents.
- The agents perform actions corresponding to the fetch/store commands.
- 30.9 The SNMP MIB and Object Names
- The Management Information Base (MIB) is the set of all objects SNMP can access.
- There are separate MIB standards for each type of device.
- MIB objects have unique long hierarchical ASN.1 dotted-decimal names.
- 30.10 The Variety of MIB Variables
- Because MIB and SNMP protocols are separate, it is easy to introduce new MIB variables
when a new protocol or device is introduced.
- There are MIBs for lots of things, such as UDP, TCP, IP, ARP, Ethernet,
routers, switches, modems, and printers.
- 30.11 MIB Variables That Correspond to Arrays
- An array or table can be a MIB variable.
- Index information is appended to variable names.