- Know that the IP packet is called a datagram.
- Know the basics of the structure of an IP datagram (both IPv4 and IPv6).
- Know the basics of the structure of IP datagram header(s) (both IPv4 and IPv6).
- Understand the basics of the method used by IP routers to forward IP datagrams - how destination addresses are matched to entries in forwarding tables, using destination network addresses and masks.
- Understand that IP routers do not change the destination addresses in IP datagrams.
- Understand the limitations of the best-effort delivery service furnished by the IP protocol.
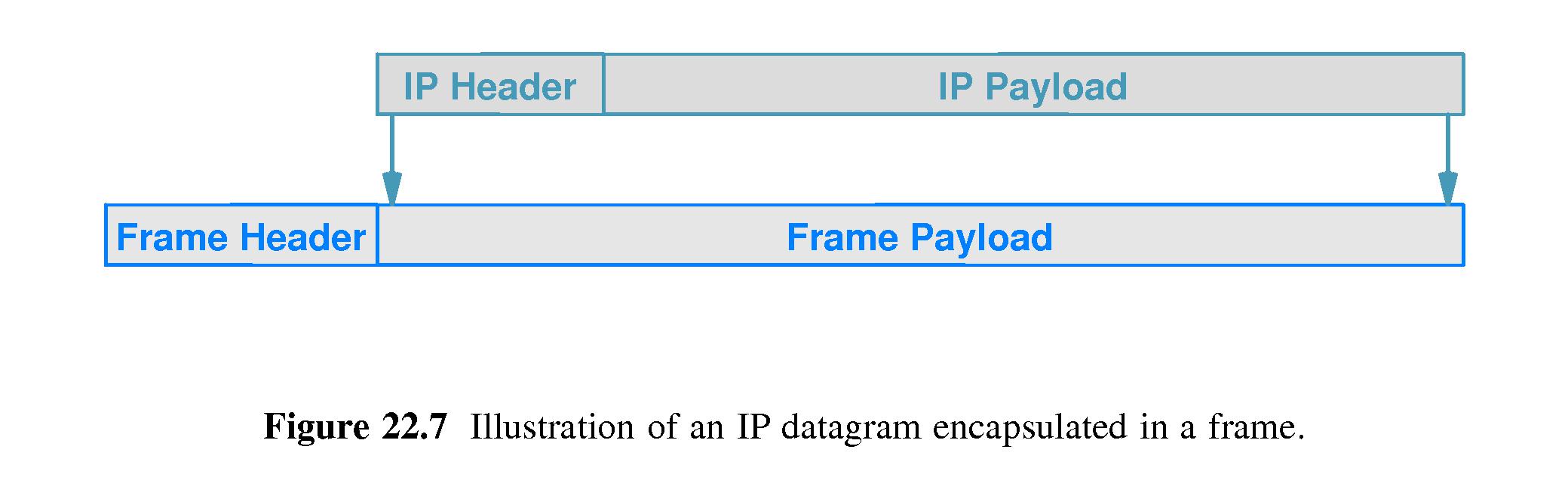
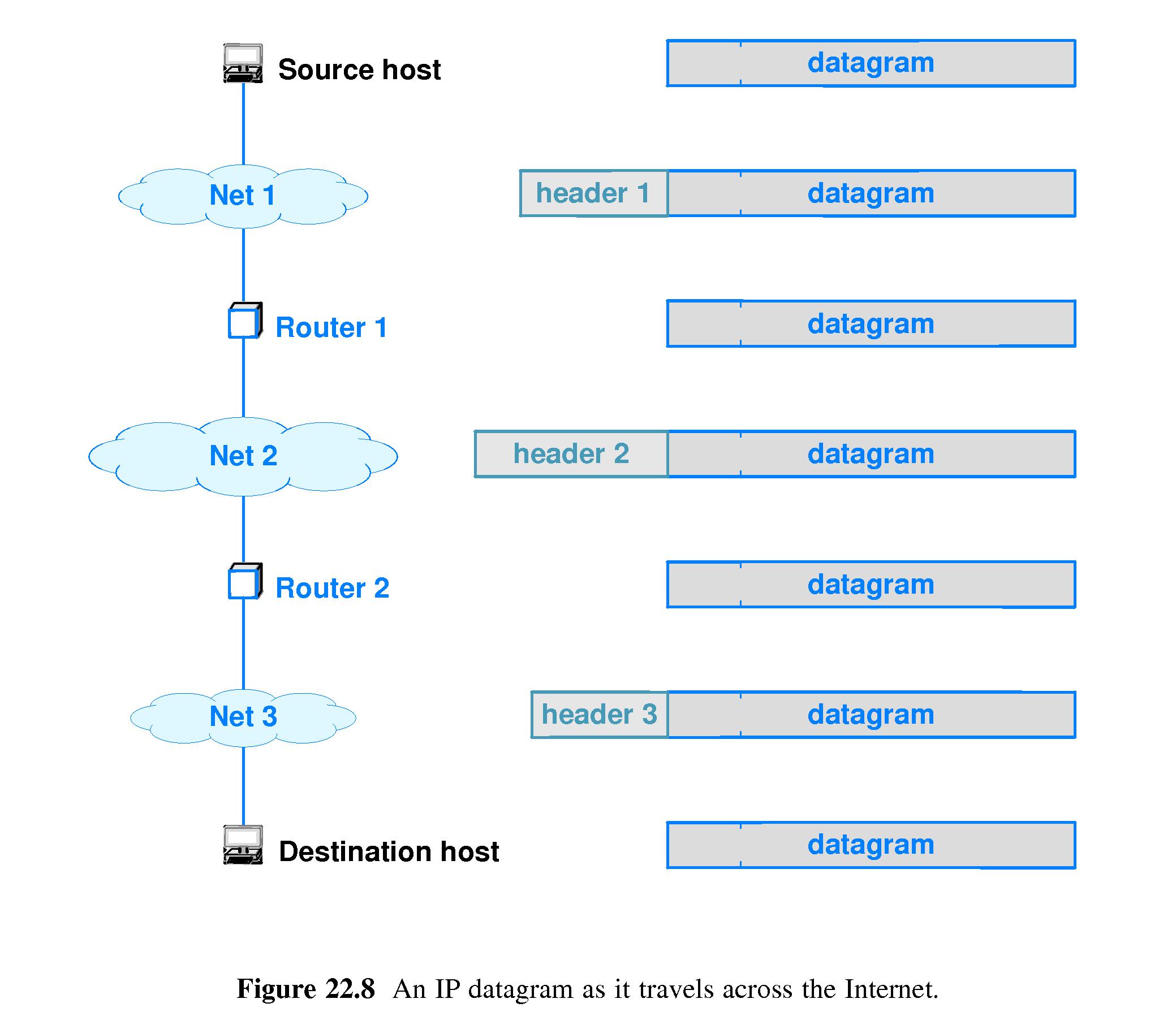
- Understand how IP datagrams are encapsulated in physical network frames for transmission across physical networks, and how things work when IP datagrams are forwarded through a series of physical networks connected by IP routers.
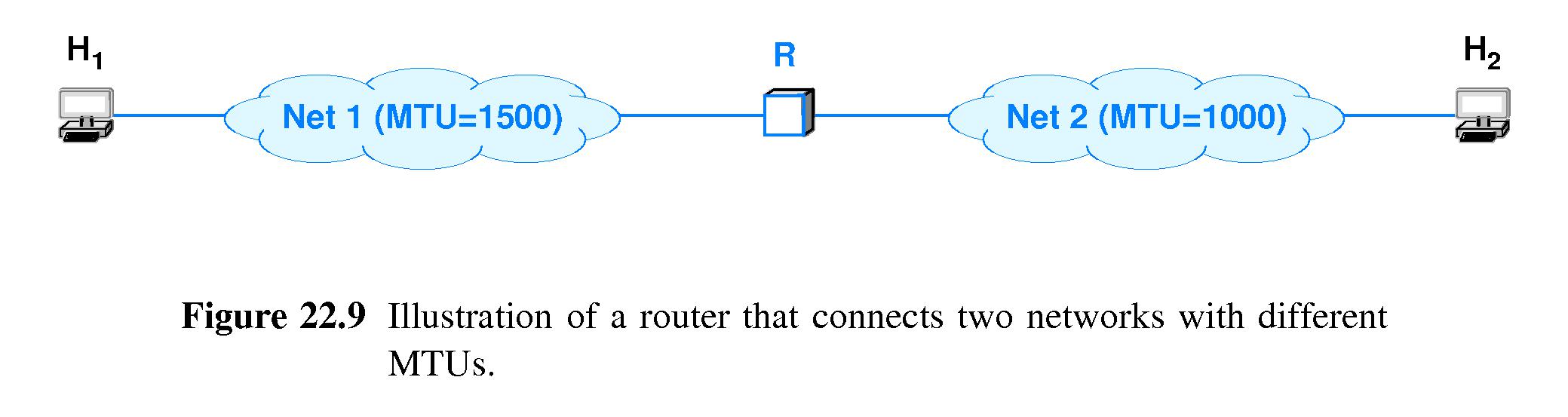
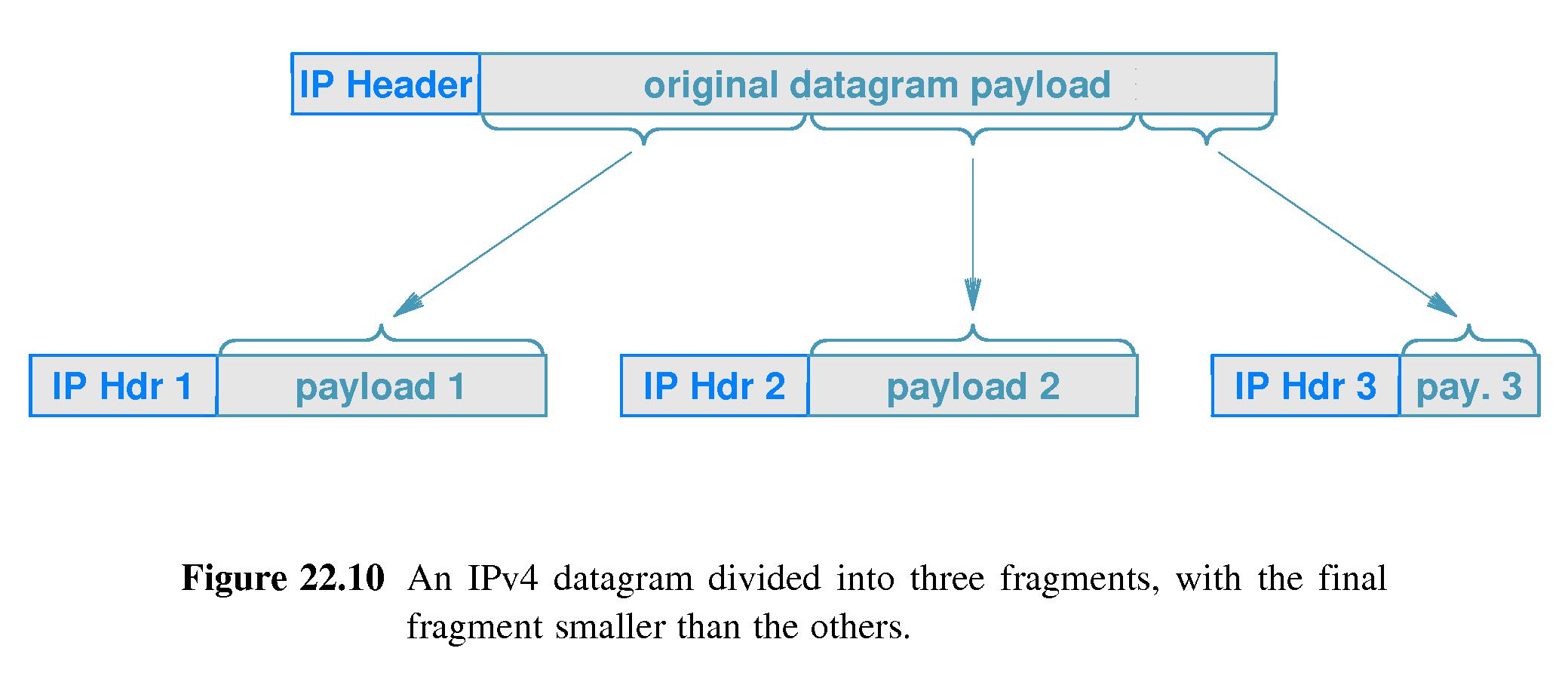
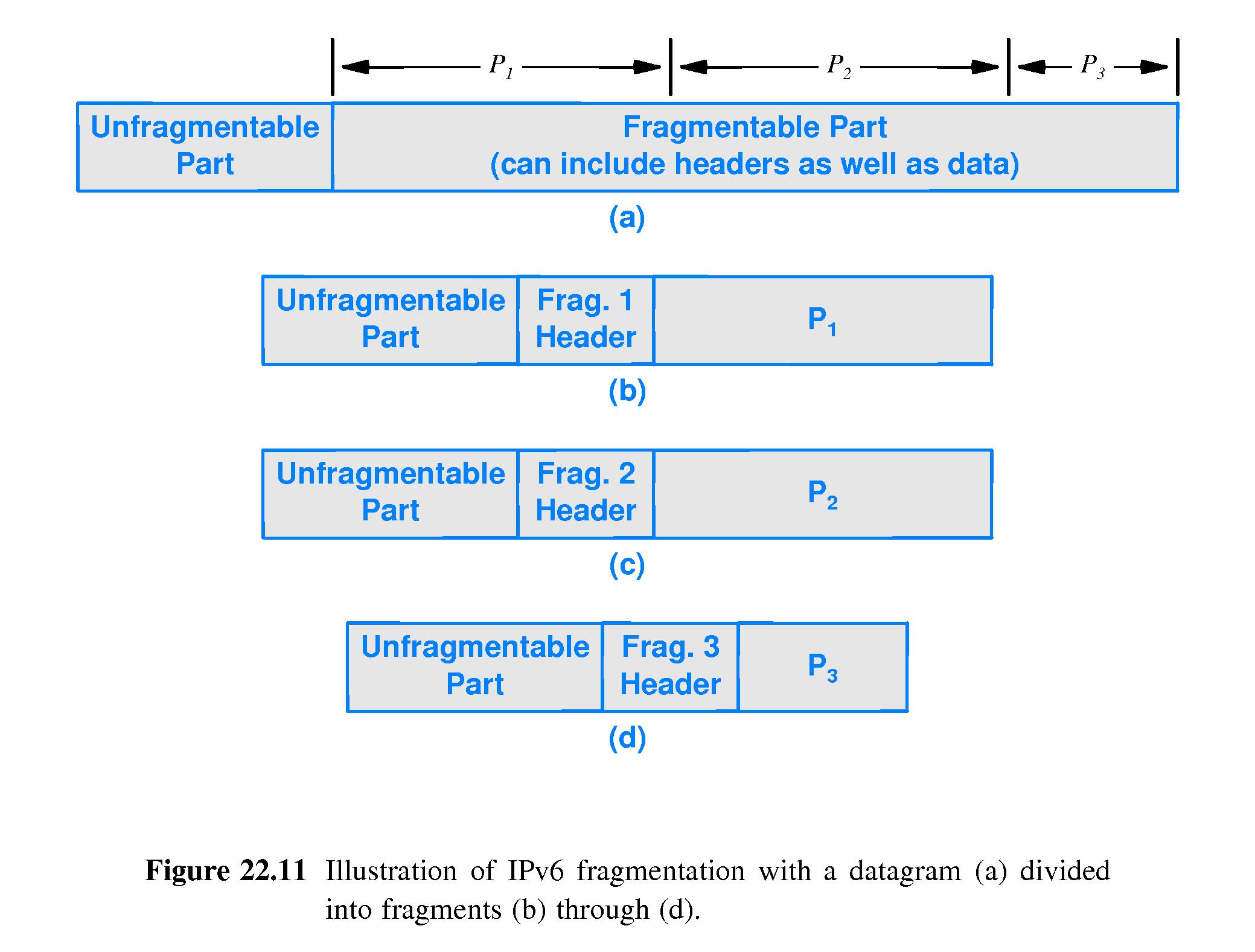
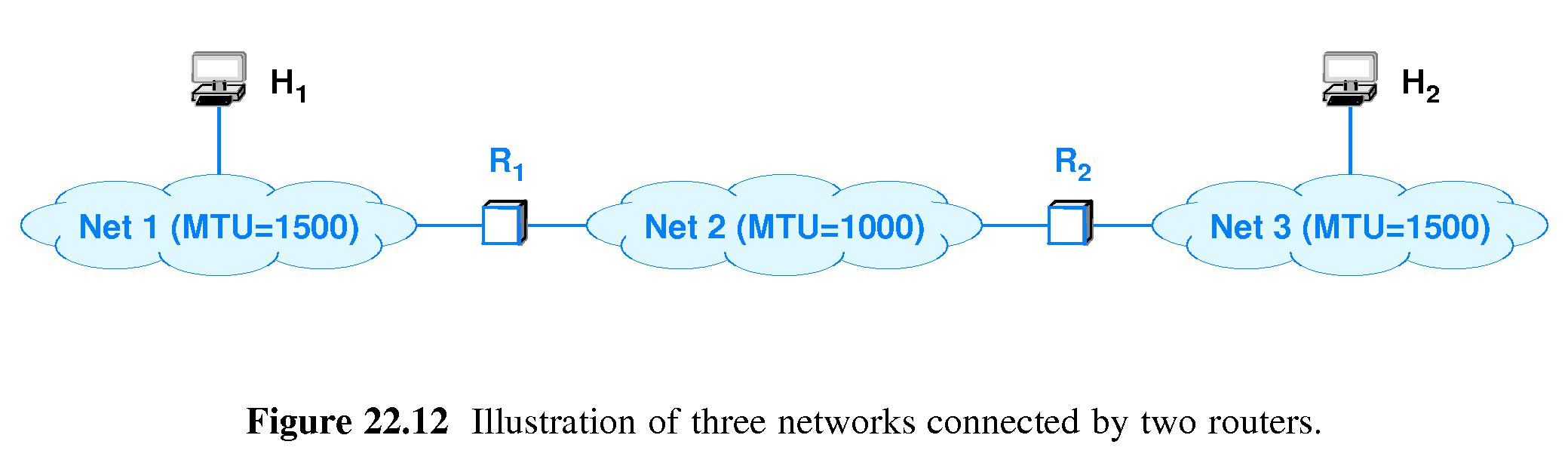
- Understand what fragmentation is and why it may be necessary.
- Understand what a network MTU is, and what a path MTU is.
- Know, under IPv4, whose responsibility it is to fragment datagrams, and whose responsibility it is to reassemble fragments.
- Know, under IPv6, whose responsibility it is to fragment datagrams, and whose responsibility it is to reassemble fragments.
- Internet communication service
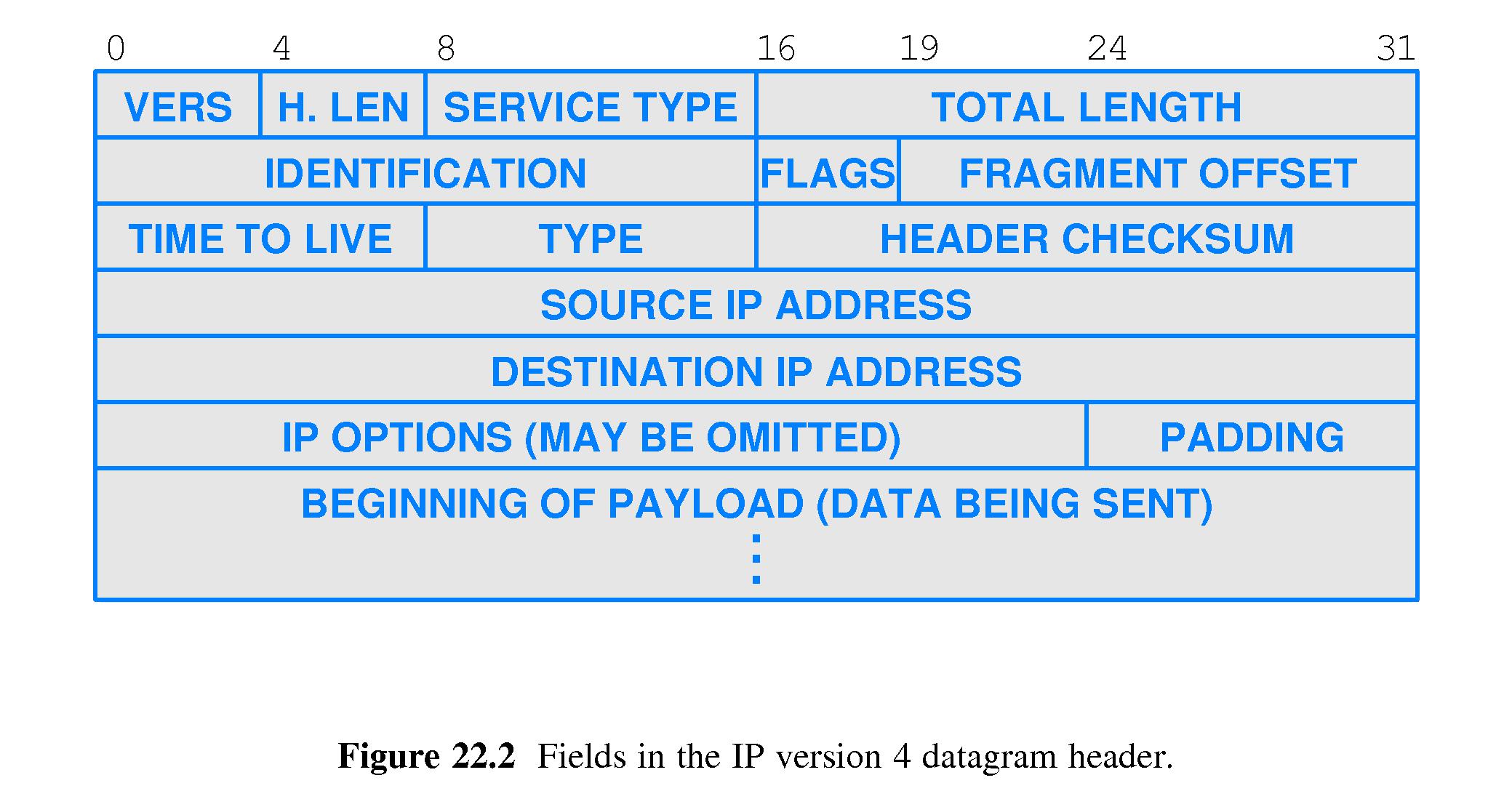
- Packet format
- Encapsulation
- Forwarding
- Fragmentation and Reassembly
- Fundamentally Internet service is connectionless and packet-based.
- However, the Internet supports reliable connection-based service, which is implemented using underlying connectionless service.
- Because of incompatibilities among network hardware features and addressing modes, implementation of the Internet requires a hardware-independent address format and packet format.
- Consequently, the Internet address and packet formats are hardware-independent.
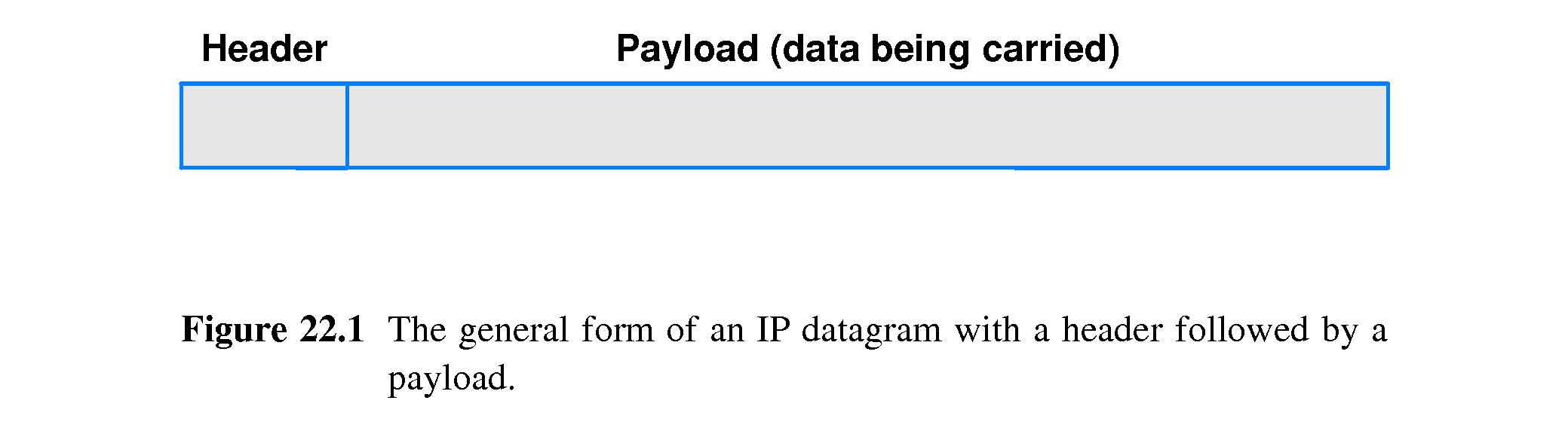
- Formally, an IP packet is called an IP datagram.
- An IP datagram consists of a header followed by a data area.
- The data area is often referred to as the payload.
- The payload can be as small as one octet (an octet is 8 bits).
- In IPv4, the combined size of the header and payload is allowed to be as large as 64K octets (but no larger).
- In IPv6, the payload itself is allowed to be up to 64K octets.
- There is a variable-sized header containing:
- Source IP address
- Destination IP address
- Other stuff
- There is a variable sized data area too -- important flexibility for the wide range of uses of IP.
- Although the IPv4 header can vary in size, each individual field within the header is fixed in size.
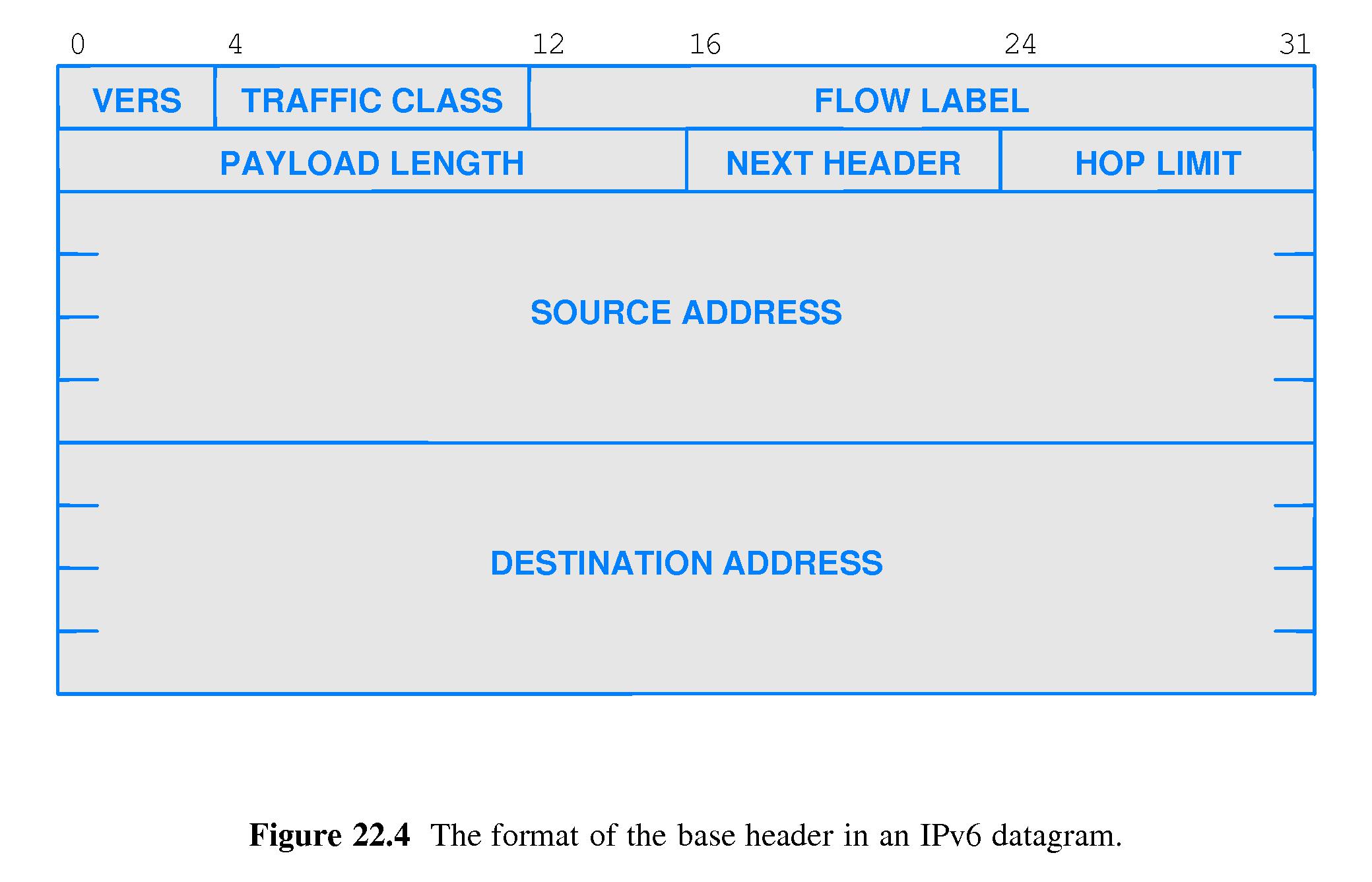
- An IPv6 header consists of:
- a base header, followed by
- one or more extension headers, followed by
- a payload.

- Most of the content consists of the source and destination addresses, both of which are 128-bit.
- Other fields are as shown in figure 22.4
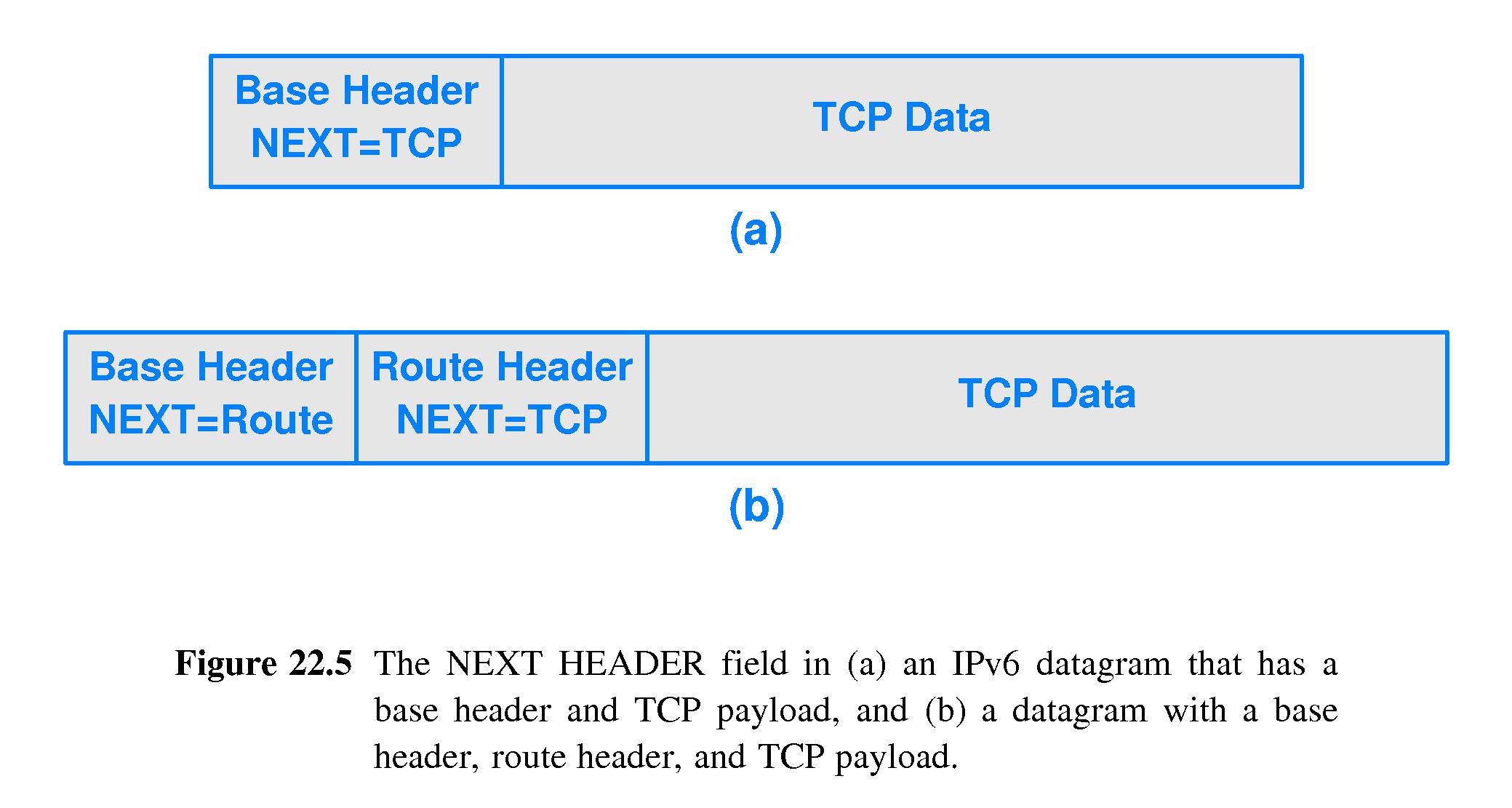
- Notably there is a Next Header field to indicate the type of information that comes next - an extension header or the payload.
- Some extension headers are variable in length, and they have a length field.
- If an IP datagram is not addressed to a local destination, it is forwarded from router to router until it reaches a router connected to the destination network. That router forwards the packet to its final destination.
- The Internet uses next-hop forwarding.
- Routers decide on the next hop based on the network prefix of the destination address.
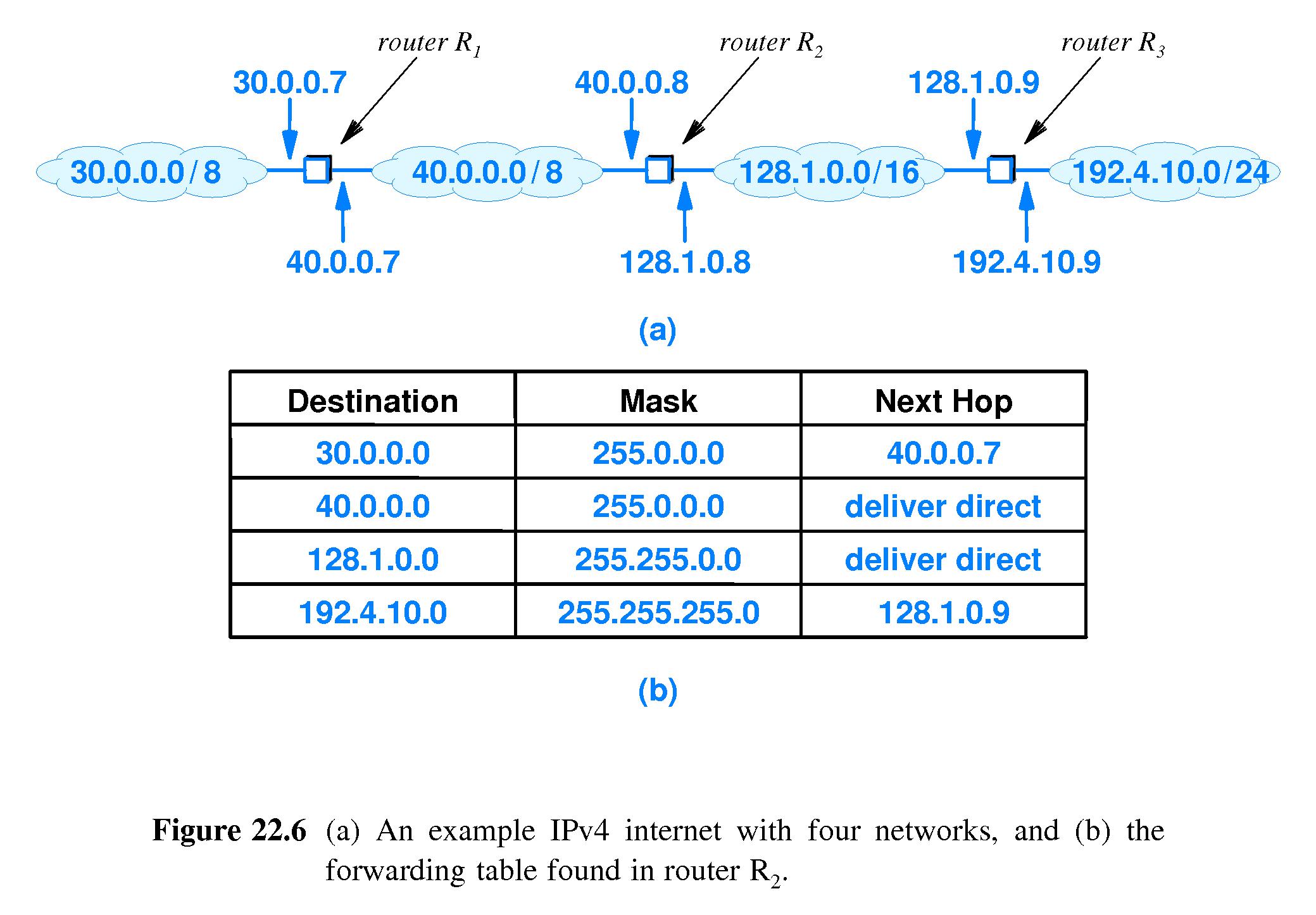
- Conceptually, each entry in a forwarding table contains three fields:
- a Destination IP network address,
- a Mask that encodes the prefix/suffix boundary of the Destination network address, and
- the IP address of a next hop to send packets addressed to that Destination network.
- To forward a packet with destination address D, the router examines
table entries until finding one such that:
Mask[i] & D == Destination[i]
When such match is found the router decides to forward the packet to NextHop[i]. - As an exercise work out the forwarding of a packet with
destination address 192.4.10.3 arriving at center router,
R2, in figure 22.6 above.
- In binary, D=192.4.10.3 is 11000000.00000100.00001010.00000011.
- The first mask, Mask[0] is, 255.0.0.0, which in binary is 11111111.00000000.00000000.00000000.
- So Mask[0] & D is
11111111.00000000.00000000.00000000 &
11000000.00000100.00001010.00000011, which equals
11000000.00000000.00000000.00000000 - The first network address in the table, Destination[0]
is 30.0.0.0, which is
00011110.00000000.00000000.00000000 in binary. That does not match Mask[0] & D. - The second network address in the table, Destination[1]
is 40.0.0.0, and Mask[1] is the same as Mask[0].
40.0.0.0 is
00101000.00000000.00000000.00000000 in binary. That does not match Mask[1] & D. - Looking at Mask[2], that's
11111111.11111111.00000000.00000000
in binary, and so Mask[2] & D is
11111111.11111111.00000000.00000000 &
11000000.00000100.00001010.00000011, which equals
11000000.00000100.00000000.00000000. Destination[2] is 128.1.0.0, which is
10000000.00000001.00000000.00000000 in binary. Destination[2] does not match Mask[2] & D. - Finally, Mask[3] is
11111111.11111111.11111111.00000000
in binary, and so Mask[3] & D is
11111111.11111111.11111111.00000000 &
11000000.00000100.00001010.00000011, which equals
11000000.00000100.00001010.00000000. Destination[3] is 192.4.10.0, which is
11000000.00000100.00001010.00000000 in binary. Destination[3] DOES match Mask[3] & D. Therefore we should route the datagram with destination address D to the next hop address in row #3, which is 128.1.0.9.